Decoding the Radiant Capital Heist: A Complete Evaluation of the $4.5 Million Cyberattack
Abstract
On January 3, 2024, Radiant Capital, a cross-chain lending protocol on Arbitrum, was exploited for about $4.5 million price of ETH. The hack primarily resulted from vulnerabilities within the sensible contract code and leveraged present rounding points within the codebase.
About Challenge:
Radiant Capital (RDNT) is a decentralized finance (DeFi) undertaking that goals to consolidate fragmented liquidity throughout a number of lending protocols and chains. For extra data, take a look at their web site.
Vulnerability Evaluation & Affect:
On-Chain Particulars:
Attacker Handle :- 0x826d5f4d8084980366f975e10db6c4cf1f9dde6d
Assault Contract:- 0x39519c027b503f40867548Fb0c890b11728faA8F
Susceptible Contract:- 0xF4B1486DD74D07706052A33d31d7c0AAFD0659E1
Assault Transaction:-0x1ce7e9a9e3b6dd3293c9067221ac3260858ce119ecb7ca860eac28b2474c7c9b
The Root Trigger :-
The foundation explanation for the incident with the Radiant Capital undertaking was a flaw in the best way they calculated token portions. This calculation concerned two principal parts: precision enlargement and rounding. Right here’s a simplified clarification of each the basis trigger and the way the vulnerability was exploited:
- Precision Enlargement and Rounding in Calculation: The calculation technique utilized by Radiant Capital concerned increasing the precision of numbers (making them extra exact) after which rounding them. They used a components that may be summarized as (a * RAY + b/2) / b, the place RAY is a big quantity (10²⁷) used to develop precision.
- Exploitation of the Components: The attacker took benefit of this components. The vulnerability lay within the dealing with of the variables ‘a’ and ‘b’. The important thing right here is the connection between the scale of ‘a’ and ‘b’. When ‘b’ is considerably smaller than ‘a’, the rounding error is tiny and negligible. Nonetheless, when ‘b’ is analogous in dimension to ‘a’, the error turns into substantial.
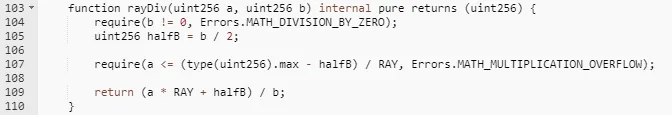
3. Manipulation of Values by Attacker: Within the assault, the perpetrator manipulated the worth of ‘b’ to be near ‘a’. This brought on a major rounding error. As an illustration, if b = 3 and a * RAY = 10000, the computed result’s 3333, which is 1/10000 lower than the true worth. Within the case of a * RAY = 10000 and b = 3000, the computed result’s 3, which is 1/10 of the true worth. The computation on this occasion equals 3/2.0001 = 1, on account of the attacker manipulating the worth of b to have an identical magnitude to a. There’s a 1/3 distinction between the calculated and precise values.
4. Affect of the Assault: By intentionally setting ‘a’ and ‘b’ to be shut in magnitude, the attacker made the system spherical off numbers in a manner that was considerably totally different from their precise worth. This allowed the attacker to artificially develop revenue margins.
Assault Course of
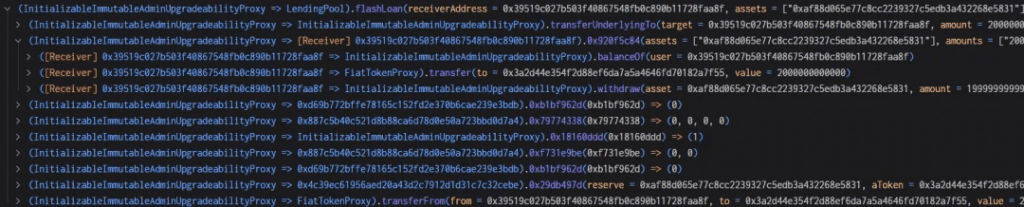
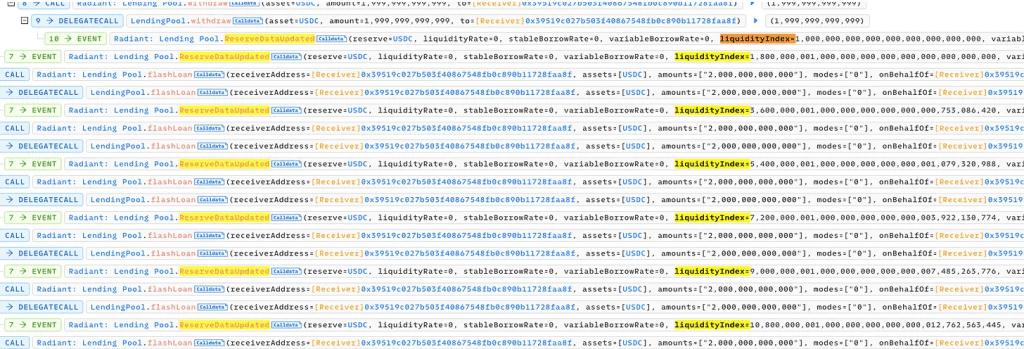
- To start the assault, the attacker first obtained a 3 million USDC flash mortgage via AAVE.
2. The attacker acquired two million rUSDCn token certificates in trade for the pledge of two million USDC to the Radiant contract.
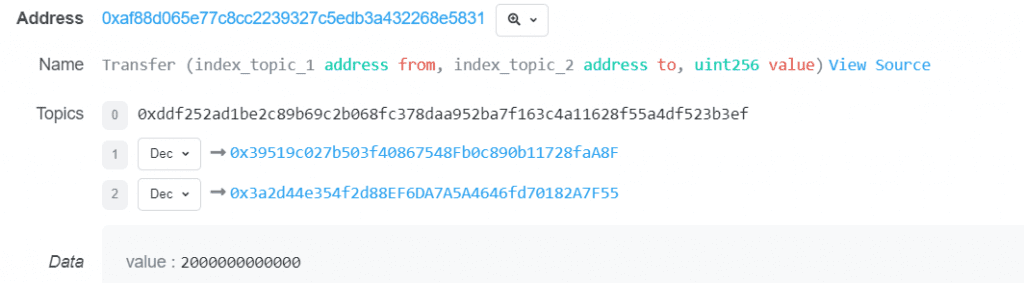
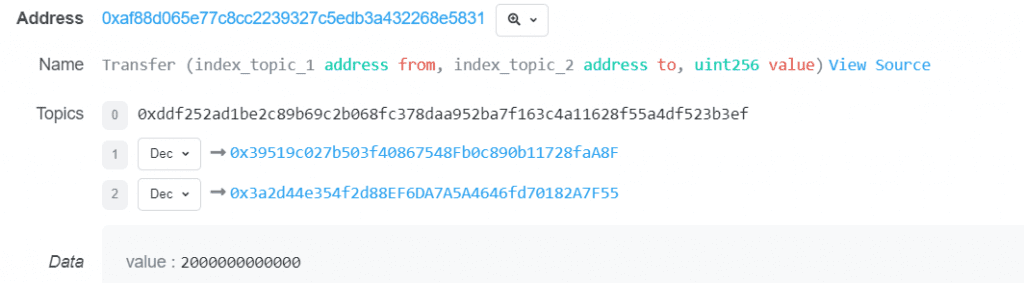
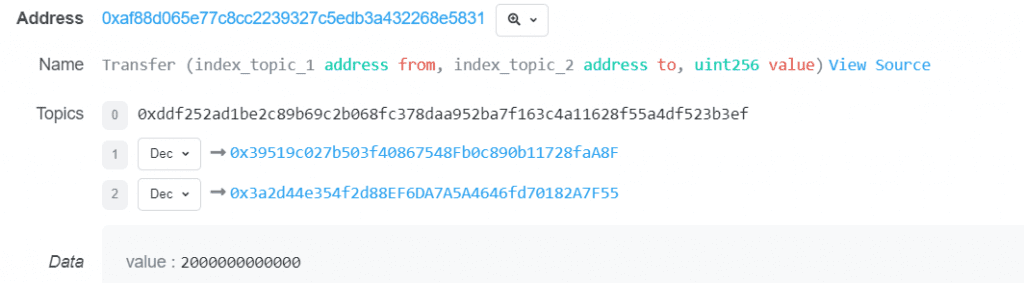
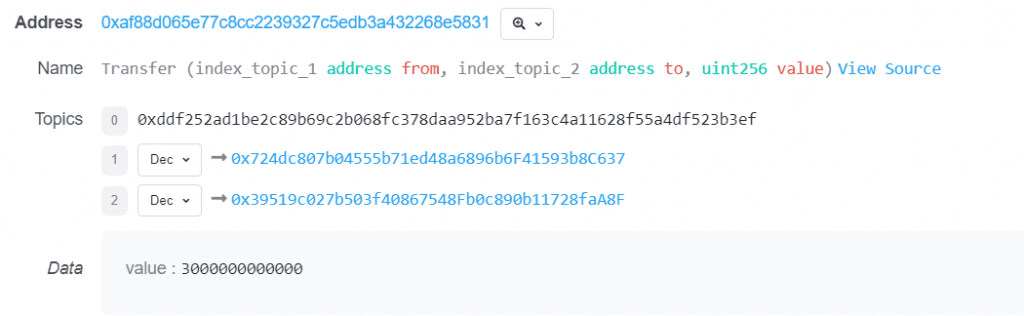
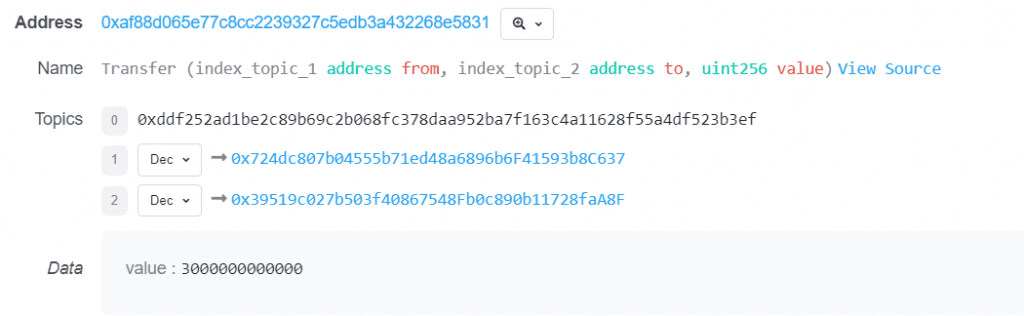
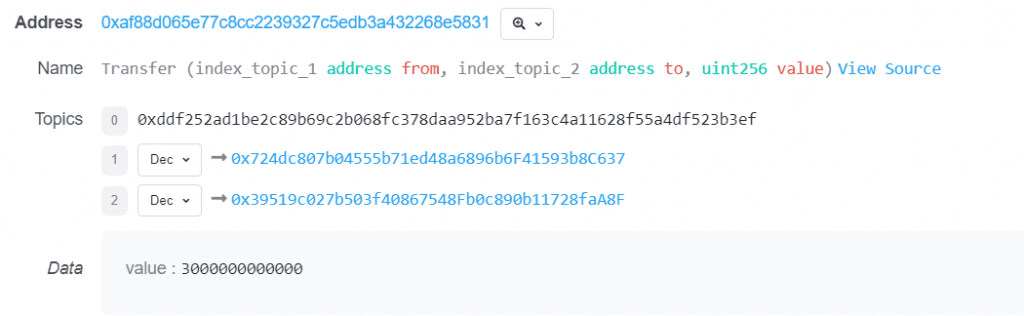
3. The attacker borrowed two million USDC utilizing a flash mortgage obtained via the Radiant contract. Within the callback perform, the pledged USDC from the second step was extracted concurrently with the reimbursement of $2 million USDC. The attacker’s USDC was transferred into the contract by the flash mortgage perform, which is also referred to as the transferfrom perform. A 9/10000 charge was collected as liquidity for the pool.
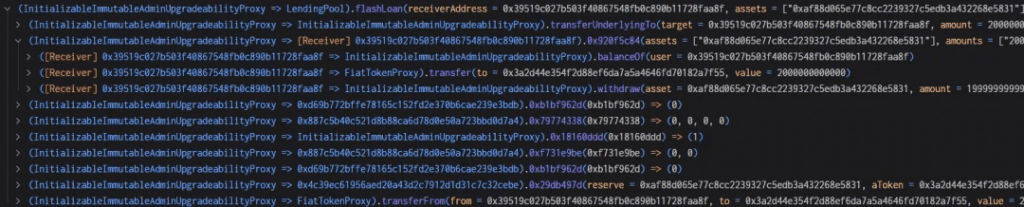
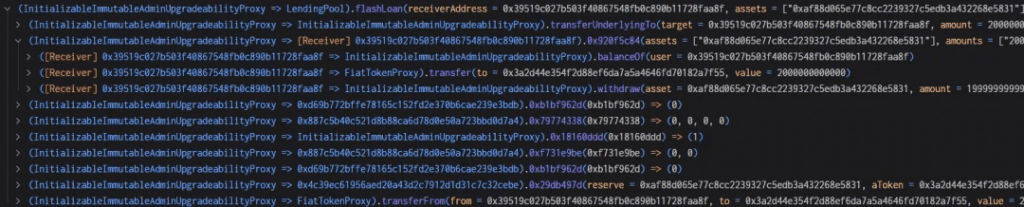
4. The result of this transaction was a manipulated liquidity index set at *271800000000.999999999999998631966035920 1e27. This worth considerably surpassed the preliminary 1e27 noticed earlier than the manipulative actions occurred.
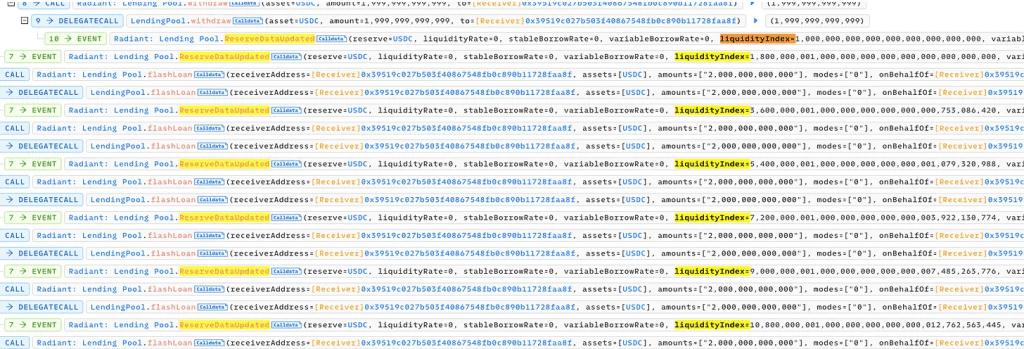
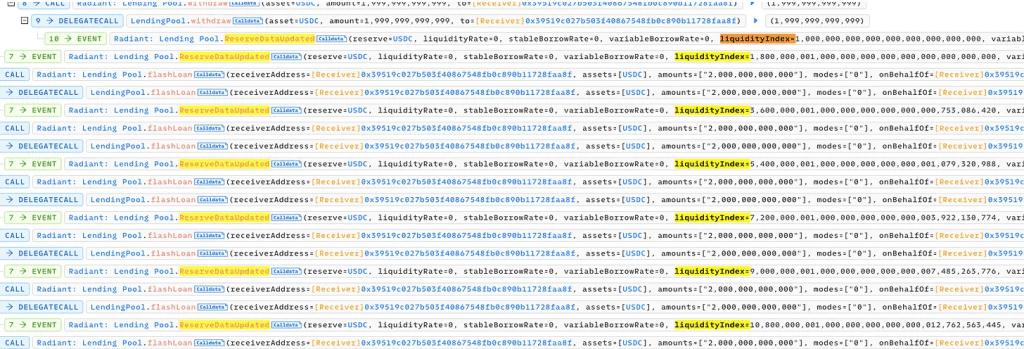
5. The attacker then made a contemporary contract and funded it with 543,600 USDC. Rounding management is made simpler by the truth that this quantity is equal to twice the liquidityIndex worth from step 4. The attacker pledged all 543,600 USDC into the Radiant contract, acquiring an equal quantity of rUSDCn.



6. The assailant took out 407,700 USDC. As beforehand said, 407,700 rUSDCn ought to have been burned; nevertheless, the burn perform required precise enlargement and rounding computations. The result’s 1/3 lower than the precise worth, 40770000000000000000000000000000000/271800000000999999999999998631966035920 = 1.49999999, however rounding produces a 1. The attacker was capable of withdraw 407,700 USDC as a result of, as may be seen under, solely 271,800 was burned versus 407,700.
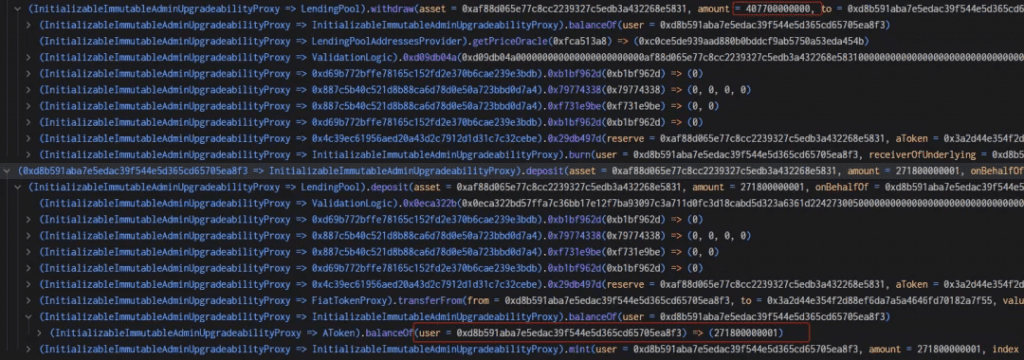
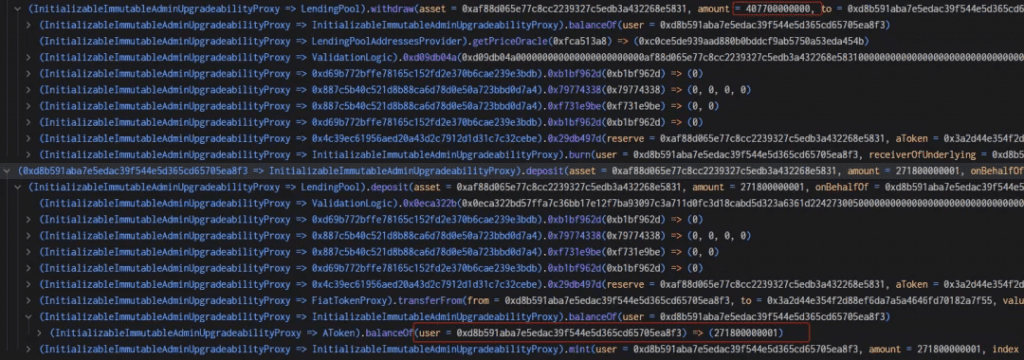
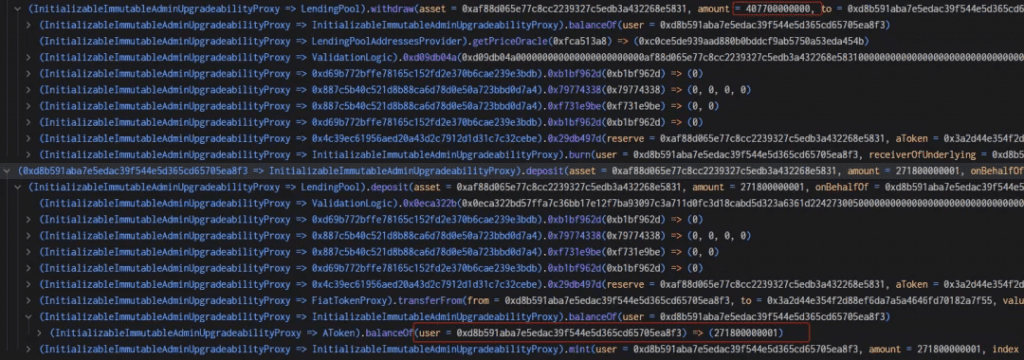
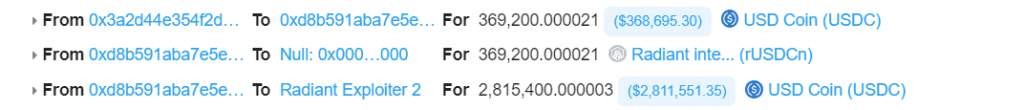
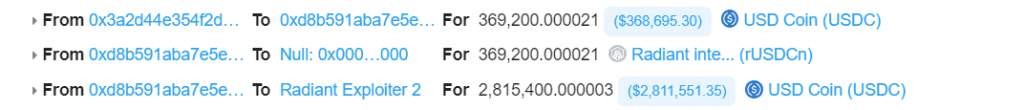
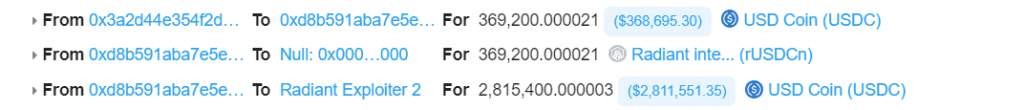
7 . The attacker then returns 271 800 USDC (+ 1 wei) to the account. The rayDiv now equals one wei fairly than zero because of the further wei. By depositing 271 800 USDC, the attacker positive aspects again 1 wei of the USDC aToken and is ready to repeat the withdraw and re-deposit cycle. For a complete of about 2.8 million USDC, the attacker should retrieve the two million USDC that was transferred into the contract in the 1st step, the 271k in flash mortgage charges, and the 543k that was deposited at first of step three. At a price of 135 900 USDC (407k — 271k) per iteration, the restoration happens. There are 18 iterations netting 2 446 200 USDC and a last withdraw of 369 200 USDC for a complete of two 815 400 USDC, so near 2.8 million which was the preliminary ballpark.



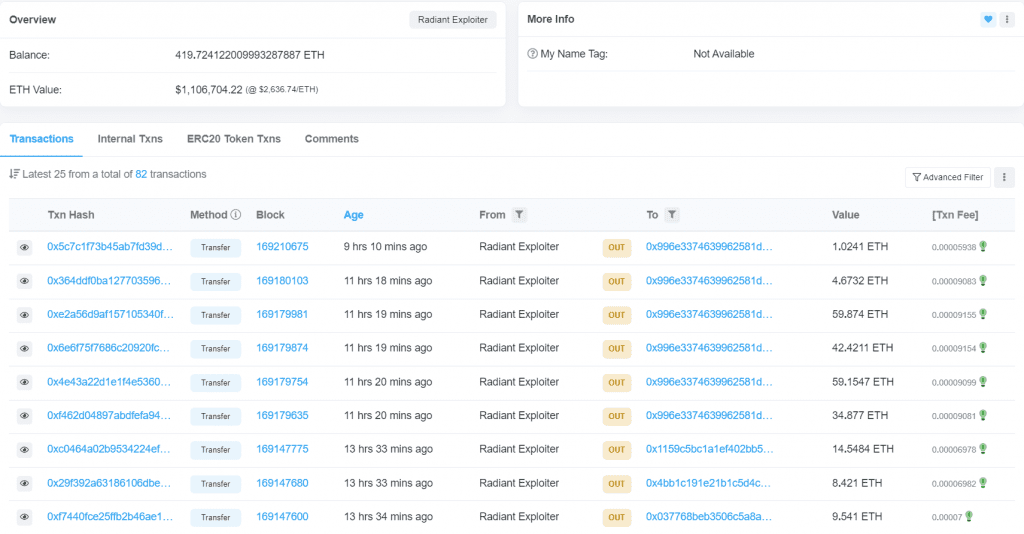
8. The hacker fled with the stolen ninety-plus WETH, recovered all the USDC that was deposited, and paid again the AAVE flash loaHacks are repeated in two following transactions (right here and right here) with bigger quantities (906 WETH extraction every) for a complete of over 1900 WETH stolen.
After the Exploit➖
Following the exploit, the Radiant Capital acknowledged the hack through their Twitter determined to briefly droop lending and borrowing markets on the platform as a precautionary measure.
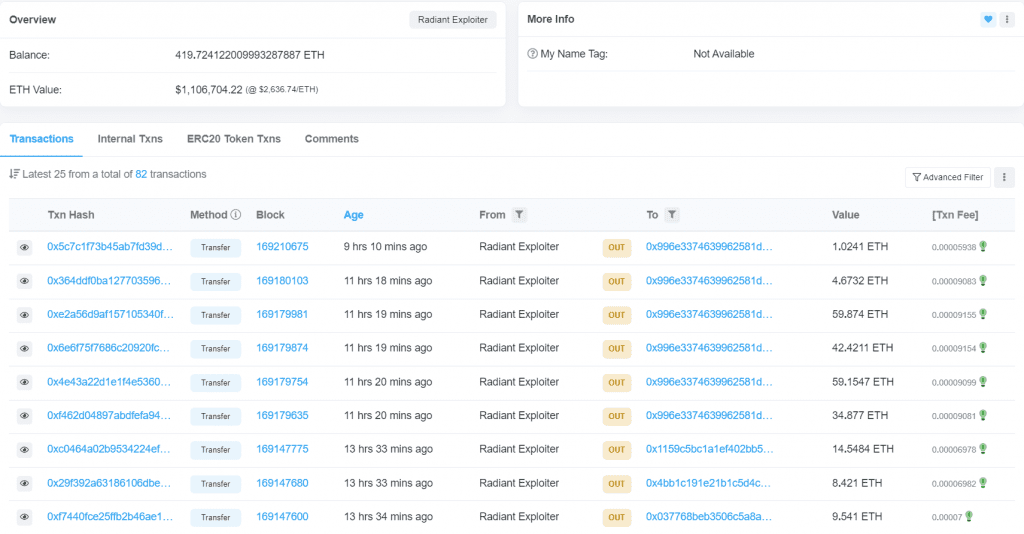
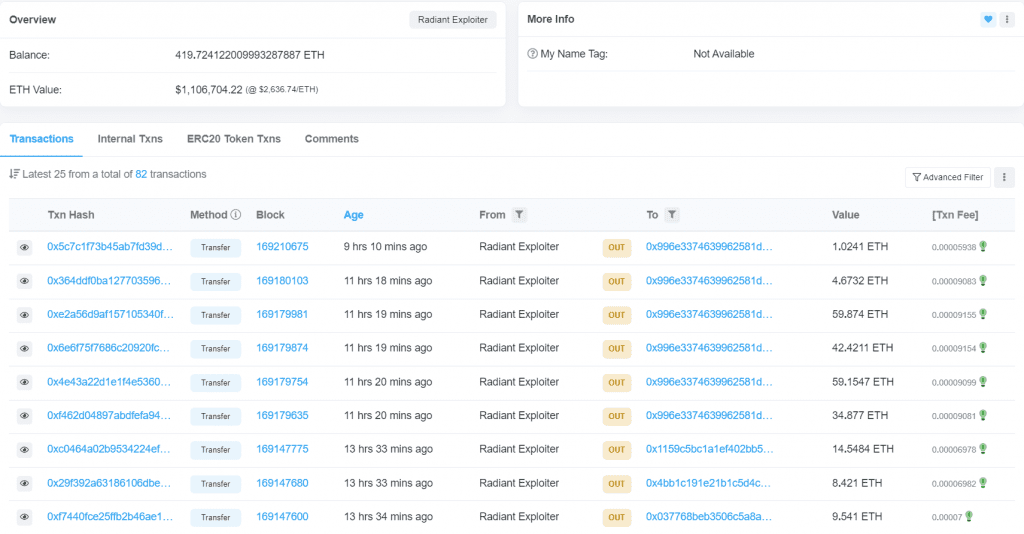
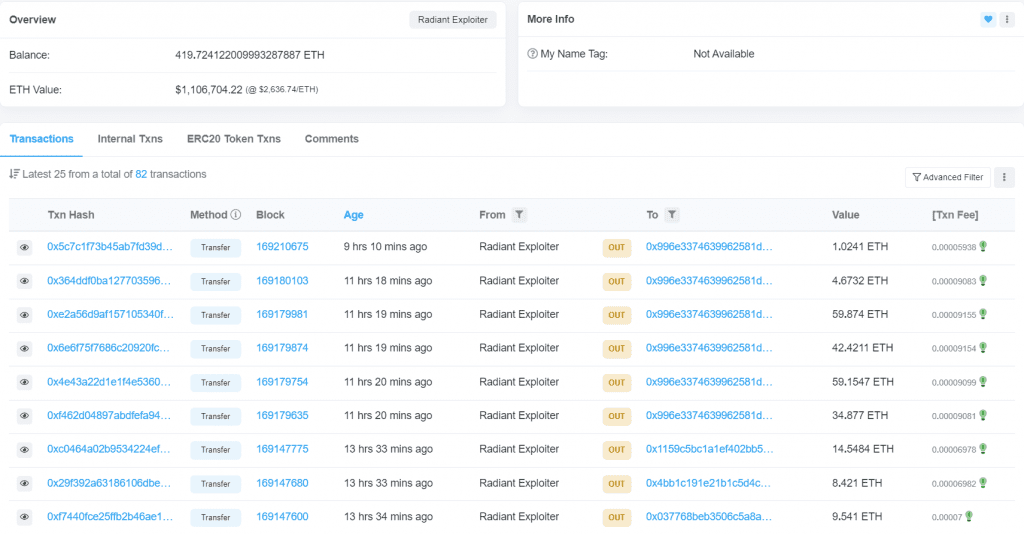
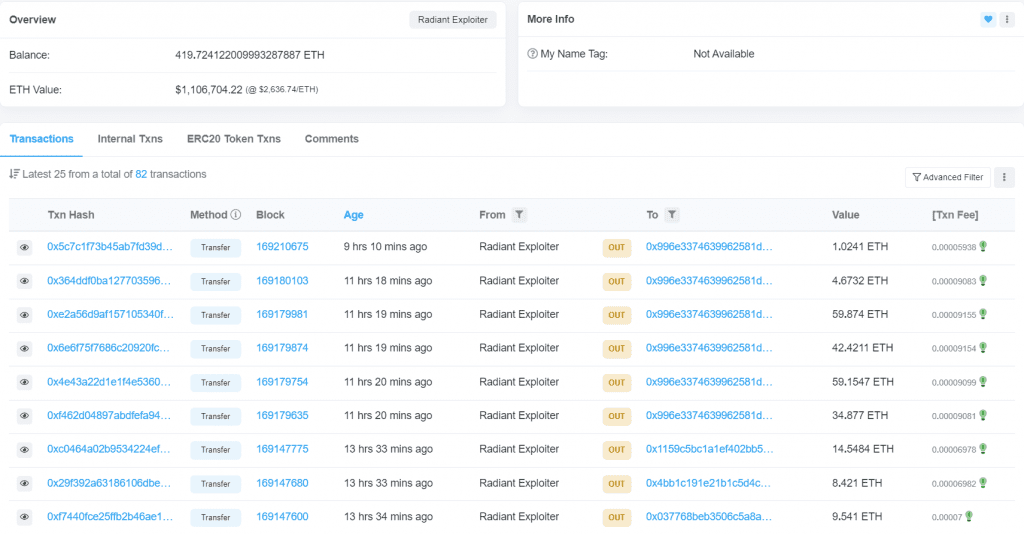
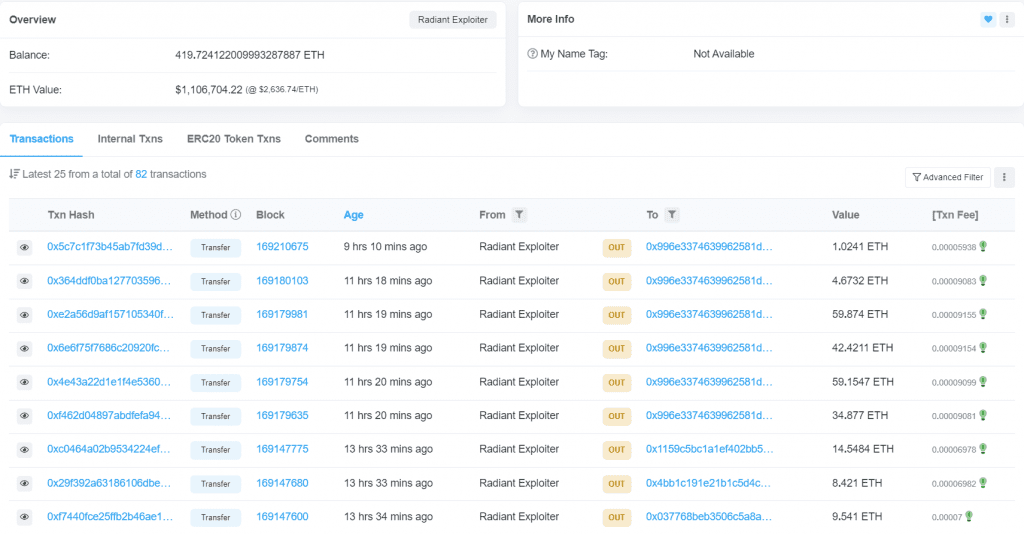
Funds Monitoring ➖Following the safety breach, the 1902 ETH that was stolen stayed within the hacker’s deal with with none exercise. As of now, the present stability is 419 ETH, because the hacker is step by step shifting the funds.
Timeline
- Jan 02, 18:53:23: The pool initialization happens with inadequate information.
- Jan 02, 18:53:38: The attacker executes a flash mortgage, manipulating the liquidity index.
- Jan 02, 18:53:46 to 18:53:49: The attacker exploits a rounding error, withdrawing from the pool.
- Jan 3, 2024, 00:14 AM UTC: The Radiant Capital group receives notification of the exploit from the attacker. They promptly paused the protocol and initiated an investigation.
- Jan 3, 2024, 08:05 PM UTC: The Radiant Capital group recognized the basis explanation for the exploit.
- Jan 4, 2024: The pool paused because the Radiant Capital group continued to handle the exploit and assess mandatory remedial actions.
The Urgency of Web3 Safety within the Present Situation
As 2024 begins, now we have witnessed 4 high-value theft instances. (Discover QuillMonitor, the web3 hacks & vulnerability software, and analyze actual assaults from 2020 onwards.) This sequence of occasions serves as a reminder that within the Web3 ecosystem, safety precautions stay essential! To forestall such vulnerabilities, the perfect Good Contract auditors should study the Good Contracts for logical points. QuillAudits stands on the forefront of this area, providing top-notch cybersecurity options that safeguard hundreds of thousands in property. Our group of specialists is adept at using superior instruments and methods to make sure the best stage of safety on your Web3 tasks.
Accomplice with QuillAudits :
Enthusiastic about collaborating with QuillAudits? Discover our partnership alternatives designed to reinforce Web3 safety throughout the ecosystem:
5 Views

