Blockchains are a strong know-how, as common readers of the weblog already seemingly agree. They permit for a lot of interactions to be codified and carried out in a manner that significantly will increase reliability, removes enterprise and political dangers related to the method being managed by a central entity, and reduces the necessity for belief. They create a platform on which purposes from totally different firms and even of various sorts can run collectively, permitting for very environment friendly and seamless interplay, and depart an audit path that anybody can examine to ensure that all the pieces is being processed accurately.
Nevertheless, after I and others discuss to firms about constructing their purposes on a blockchain, two main points at all times come up: scalability and privateness. Scalability is a major problem; present blockchains, processing 3-20 transactions per second, are a number of orders of mangitude away from the quantity of processing energy wanted to run mainstream cost techniques or monetary markets, a lot much less decentralized boards or international micropayment platforms for IoT. Fortuitously, there are options, and we’re actively engaged on implementing a roadmap to creating them occur. The opposite main downside that blockchains have is privateness. As seductive as a blockchain’s different benefits are, neither firms or people are significantly eager on publishing all of their data onto a public database that may be arbitrarily learn with none restrictions by one’s personal authorities, international governments, members of the family, coworkers and enterprise rivals.
In contrast to with scalability, the options for privateness are in some instances simpler to implement (although in different instances a lot a lot tougher), lots of them suitable with at present current blockchains, however they’re additionally a lot much less satisfying. It is a lot tougher to create a “holy grail” know-how which permits customers to do completely all the pieces that they will do proper now on a blockchain, however with privateness; as a substitute, builders will in lots of instances be compelled to cope with partial options, heuristics and mechanisms which are designed to deliver privateness to particular lessons of purposes.
The Holy Grail
First, allow us to begin off with the applied sciences that are holy grails, in that they really do provide the promise of changing arbitrary purposes into absolutely privacy-preserving purposes, permitting customers to learn from the safety of a blockchain, utilizing a decentralized community to course of the transactions, however “encrypting” the info in such a manner that regardless that all the pieces is being computed in plain sight, the underlying “that means” of the knowledge is totally obfuscated.
Probably the most highly effective know-how that holds promise in route is, after all, cryptographically safe obfuscation. Normally, obfuscation is a manner of turning any program right into a “black field” equal of this system, in such a manner that this system nonetheless has the identical “inner logic”, and nonetheless offers the identical outputs for a similar inputs, nevertheless it’s unattainable to find out some other particulars about how this system works.
Consider it as “encrypting” the wires inside the field in such a manner that the encryption cancels itself out and finally has no impact on the output, however does have the impact of creating it completely unattainable to see what’s going on inside.
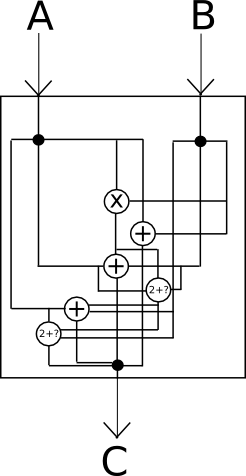
Sadly, completely good black-box obfuscation is mathematically identified to be unattainable; it seems that there’s at all times at the least one thing that you could get extract out of a program by taking a look at it past simply the outputs that it offers on a particular set of inputs. Nevertheless, there’s a weaker normal referred to as indistinguishability obfuscation that we are able to fulfill: primarily, given two equal applications which were obfuscated utilizing the algorithm (eg. x = (a + b) * c and x = (a * c) + (b * c)), one can not decide which of the 2 outputs got here from which authentic supply. To see how that is nonetheless highly effective sufficient for our purposes, take into account the next two applications:
- y = 0
- y = signal(privkey, 0) – signal(privkey, 0)
One simply returns zero, and the opposite makes use of an internally contained non-public key to cryptographically signal a message, does that very same operation one other time, subtracts the (clearly equivalent) outcomes from one another and returns the consequence, which is assured to be zero. Despite the fact that one program simply returns zero, and the opposite comprises and makes use of a cryptographic non-public key, if indistinguishability is happy then we all know that the 2 obfuscated applications can’t be distinguished from one another, and so somebody in possession of the obfuscated program positively has no manner of extracting the non-public key – in any other case, that may be a manner of distinguishing the 2 applications. That is some fairly highly effective obfuscation proper there – and for about two years we have identified methods to do it!
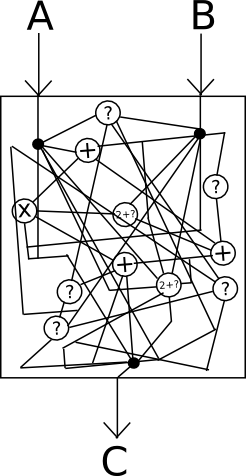
So, how can we use this on a blockchain? Here is one easy strategy for a digital token. We create an obfuscated sensible contract which comprises a non-public key, and accepts directions encrypted with the correponding public key. The contract shops account balances in storage encrypted, and if the contract desires to learn the storage it decrypts it internally, and if the contract desires to put in writing to storage it encrypts the specified consequence earlier than writing it. If somebody desires to learn a stability of their account, then they encode that request as a transaction, and simulate it on their very own machine; the obfuscated sensible contract code will examine the signature on the transaction to see if that consumer is entitled to learn the stability, and if they’re entitled to learn the stability it would return the decrypted stability; in any other case the code will return an error, and the consumer has no manner of extracting the knowledge.
Nevertheless, as with a number of different applied sciences of this sort, there may be one downside: the mechanism for doing this type of obfuscation is horrendously inefficient. Billion-factor overhead is the norm, and sometimes even extremely optimistic; a current paper estimates that “executing [a 2-bit multiplication] circuit on the identical CPU would take 1.3 * 108 years”. Moreover, if you wish to forestall reads and writes to storage from being a knowledge leak vector, you could additionally arrange the contract in order that learn and write operations at all times modify giant parts of a contract’s total state – one other supply of overhead. When, on high of that, you’ve gotten the overhead of a whole lot of nodes operating the code on a blockchain, one can rapidly see how this know-how is, sadly, not going to alter something any time quickly.
Taking A Step Down
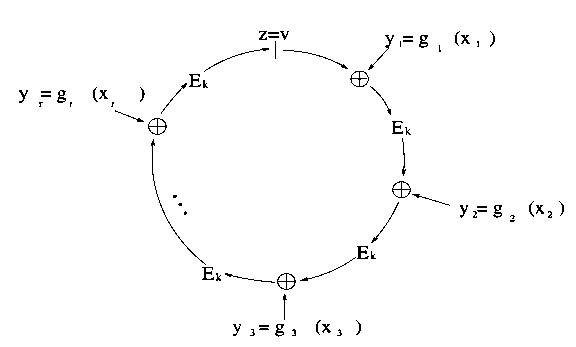
Nevertheless, there are two branches of know-how that may get you virtually so far as obfuscation, although with essential compromises to the safety mannequin. The primary is safe multi-party computation. Safe multi-party computation permits for a program (and its state) to be cut up amongst N events in such a manner that you just want M of them (eg. N = 9, M = 5) to cooperate with a view to both full the computation or reveal any inner knowledge in this system or the state. Thus, should you can belief the vast majority of the contributors to be sincere, the scheme is pretty much as good as obfuscation. If you cannot, then it is nugatory.
The mathematics behind safe multi-party computation is advanced, however a lot less complicated than obfuscation; if you’re within the technical particulars, then you may learn extra right here (and in addition the paper of Enigma, a challenge that seeks to really implement the key sharing DAO idea, right here). SMPC can be rather more environment friendly than obfuscation, the purpose that you could perform sensible computations with it, however even nonetheless the inefficiencies are very giant. Addition operations could be processed pretty rapidly, however each time an SMPC occasion performs some very small mounted variety of multiplication operations it must carry out a “diploma discount” step involving messages being despatched from each node to each node within the community. Current work reduces the communication overhead from quadratic to linear, however even nonetheless each multiplication operation brings a sure unavoidable stage of community latency.
The requirement of belief on the contributors can be an onerous one; be aware that, as is the case with many different purposes, the contributors have the power to avoid wasting the info after which collude to uncover at any future level in historical past. Moreover, it’s unattainable to inform that they’ve carried out this, and so it’s unattainable to incentivize the contributors to take care of the system’s privateness; because of this, safe multi-party computation is arguably rather more suited to non-public blockchains, the place incentives can come from outdoors the protocol, than public chains.
One other form of know-how that has very highly effective properties is zero-knowledge proofs, and particularly the current developments in “succinct arguments of information” (SNARKs). Zero-knowledge proofs permit a consumer to assemble a mathematical proof {that a} given program, when executed on some (presumably hidden) enter identified by the consumer, has a selected (publicly identified) output, with out revealing some other data. There are lots of specialised sorts of zero-knowledge proofs which are pretty simple to implement; for instance, you may consider a digital signature as a form of zero-knowledge proof displaying that the worth of a non-public key which, when processed utilizing an ordinary algorithm, could be transformed into a selected public key. ZK-SNARKs, then again, assist you to make such a proof for any operate.
First, allow us to undergo some particular examples. One pure use case for the know-how is in identification techniques. For instance, suppose that you just need to show to a system that you’re (i) a citizen of a given nation, and (ii) over 19 years outdated. Suppose that your authorities is technologically progressive, and points cryptographically signed digital passports, which embrace an individual’s identify and date of beginning in addition to a non-public and public key. You’d assemble a operate which takes a digital passport and a signature signed by the non-public key within the passport as enter, and outputs 1 if each (i) the date of beginning is earlier than 1996, (ii) the passport was signed with the federal government’s public key, and (iii) the signature is right, and outputs 0 in any other case. You’d then make a zero-knowledge proof displaying that you’ve got an enter that, when handed by means of this operate, returns 1, and signal the proof with one other non-public key that you just need to use to your future interactions with this service. The service would confirm the proof, and if the proof is right it might settle for messages signed along with your non-public key as legitimate.
You possibly can additionally use the identical scheme to confirm extra advanced claims, like “I’m a citizen of this nation, and my ID quantity isn’t on this set of ID numbers which have already been used”, or “I’ve had favorable opinions from some retailers after buying at the least $10,000 value of merchandise from them”, or “I maintain property value at the least $250,000”.
One other class of use instances for the know-how is digital token possession. With the intention to have a functioning digital token system, you don’t strictly have to have seen accounts and balances; in reality, all that you just want is a option to remedy the “double spending” downside – if in case you have 100 models of an asset, you must be capable to spend these 100 models as soon as, however not twice. With zero-knowledge proofs, we are able to after all do that; the declare that you’d zero-knowledge-prove is one thing like “I do know a secret quantity behind one of many accounts on this set of accounts which were created, and it doesn’t match any of the key numbers which have already been revealed”. Accounts on this scheme turn into one-time-use: an “account” is created each time property are despatched, and the sender account is totally consumed. If you do not need to fully eat a given account, then you could merely create two accounts, one managed by the recipient and the opposite with the remaining “change” managed by the sender themselves. That is primarily the scheme utilized by Zcash (see extra about the way it works right here).
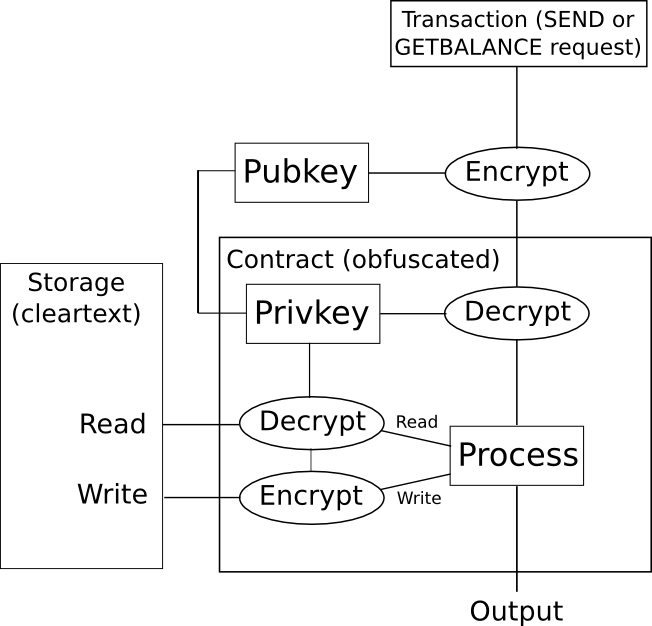
For 2-party sensible contracts (eg. consider one thing like a monetary spinoff contract negotiated between two events), the applying of zero-knowledge-proofs is pretty simple to know. When the contract is first negotiated, as a substitute of making a sensible contract containing the precise method by which the funds will ultimately be launched (eg. in a binary possibility, the method can be “if index I as launched by some knowledge supply is larger than X, ship all the pieces to A, in any other case ship all the pieces to B”), create a contract containing the hash of the method. When the contract is to be closed, both get together can themselves compute the quantity that A and B ought to obtain, and supply the consequence alongside a zero-knowledge-proof {that a} method with the proper hash offers that consequence. The blockchain finds out how a lot A and B every put in, and the way a lot they get out, however not why they put in or get out that quantity.
This mannequin could be generalized to N-party sensible contracts, and the Hawk challenge is looking for to do precisely that.
Ranging from the Different Finish: Low-Tech Approaches
The opposite path to take when attempting to extend privateness on the blockchain is to begin with very low-tech approaches, utilizing no crypto past easy hashing, encryption and public key cryptography. That is the trail that Bitcoin began from in 2009; although the extent of privateness that it offers in observe is kind of troublesome to quantify and restricted, it nonetheless clearly offered some worth.
The best step that Bitcoin took to considerably enhance privateness is its use of one-time accounts, just like Zcash, with a view to retailer funds. Similar to with Zcash, each transaction should fully empty a number of accounts, and create a number of new accounts, and it is strongly recommended for customers to generate a brand new non-public key for each new account that they intend to obtain funds into (although it’s potential to have a number of accounts with the identical non-public key). The principle profit that this brings is {that a} consumer’s funds usually are not linked to one another by default: should you obtain 50 cash from supply A and 50 cash from supply B, there isn’t a manner for different customers to inform that these funds belong to the identical particular person. Moreover, should you spend 13 cash to another person’s account C, and thereby create a fourth account D the place you ship the remaining 37 cash from certainly one of these accounts as “change”, the opposite customers can not even inform which of the 2 outputs of the transaction is the “cost” and which is the “change”.
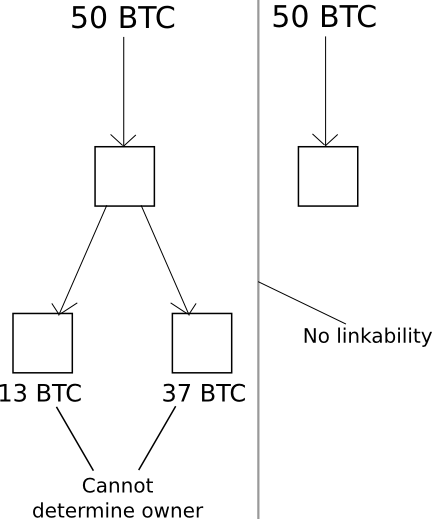
Nevertheless, there’s a downside. If, at any level sooner or later, you make a transaction consuming from two accounts on the similar time, then you definately irrevertibly “hyperlink” these accounts, making it apparent to the world that they arrive from one consumer. And, what’s extra, these linkages are transitive: if, at any level, you hyperlink collectively A and B, after which at some other level hyperlink collectively A and C, and so forth, then you definately’ve created a considerable amount of proof by which statistical evaluation can hyperlink up your total set of property.
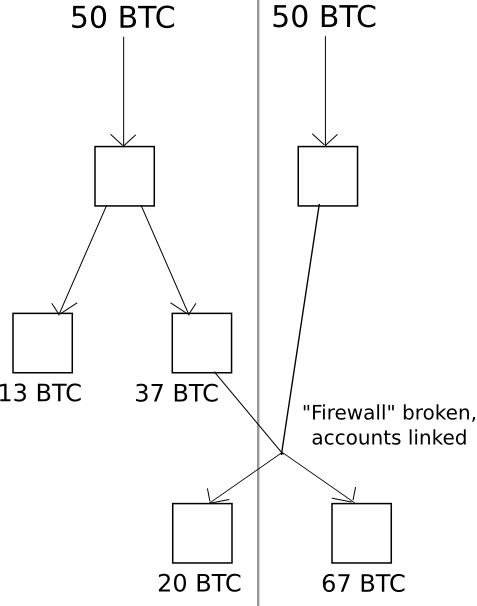
Bitcoin developer Mike Hearn got here up with a mitigation technique that reduces the chance of this occurring referred to as merge avoidance: primarily, a elaborate time period for attempting actually actually laborious to reduce the variety of instances that you just hyperlink accounts collectively by spending from them on the similar time. This positively helps, however even nonetheless, privateness inside the Bitcoin system has confirmed to be extremely porous and heuristic, with nothing even near approaching excessive ensures.
A considerably extra superior method is named CoinJoin. Primarily, the CoinJoin protocol works as follows:
- N events come collectively over some nameless channel, eg. Tor. They every present a vacation spot deal with D[1] … D[N].
- One of many events creates a transaction which sends one coin to every vacation spot deal with.
- The N events sign off after which individually log in to the channel, and every contribute one coin to the account that the funds will likely be paid out from.
- If N cash are paid into the account, they’re distributed to the vacation spot addresses, in any other case they’re refunded.
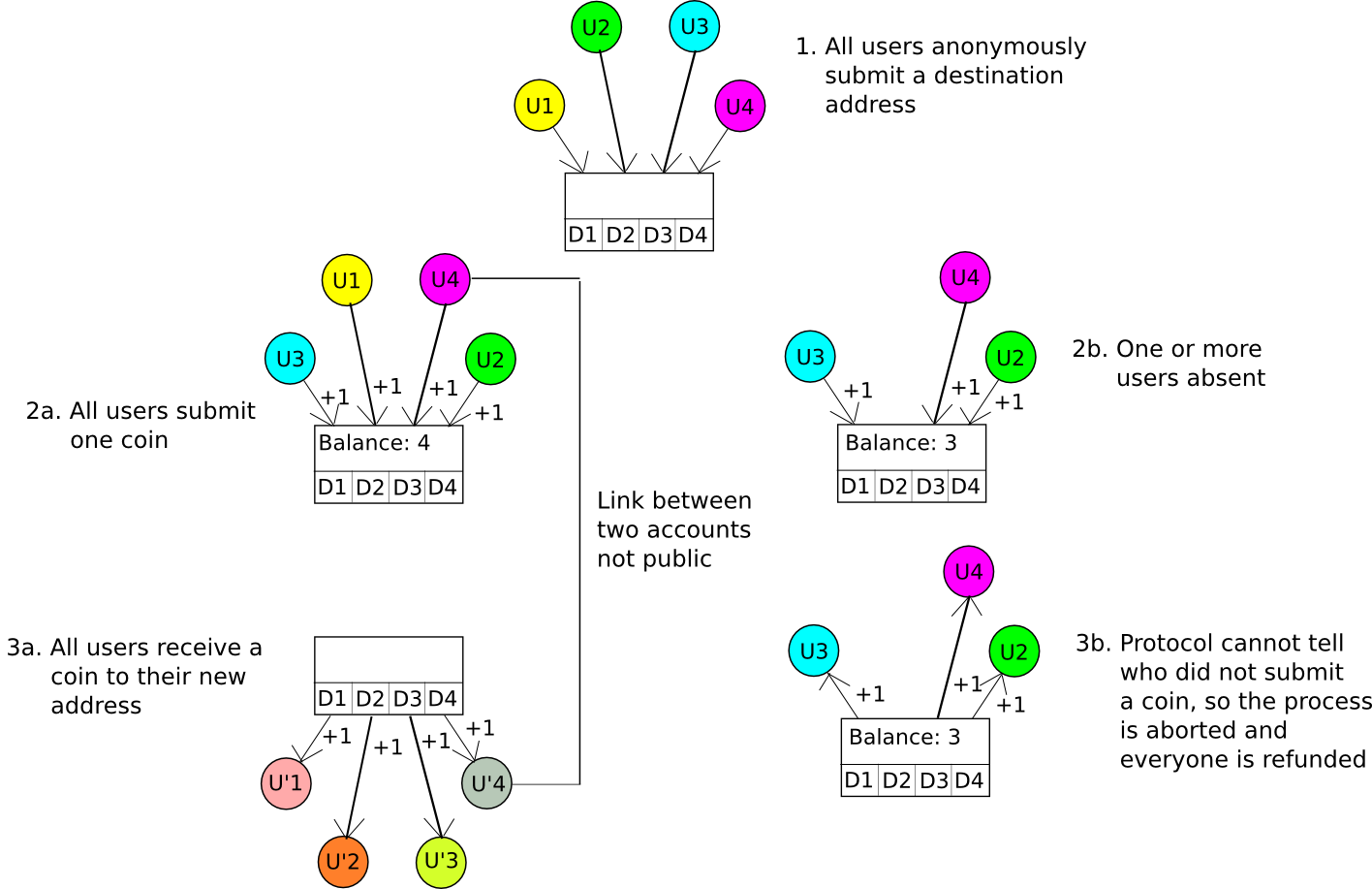
If all contributors are sincere and supply one coin, then everybody will put one coin in and get one coin out, however nobody will know which enter maps to which output. If at the least one participant doesn’t put one coin in, then the method will fail, the cash will get refunded, and all the contributors can attempt once more. An algorithm just like this was applied by Amir Taaki and Pablo Martin for Bitcoin, and by Gavin Wooden and Vlad Gluhovsky for Ethereum.
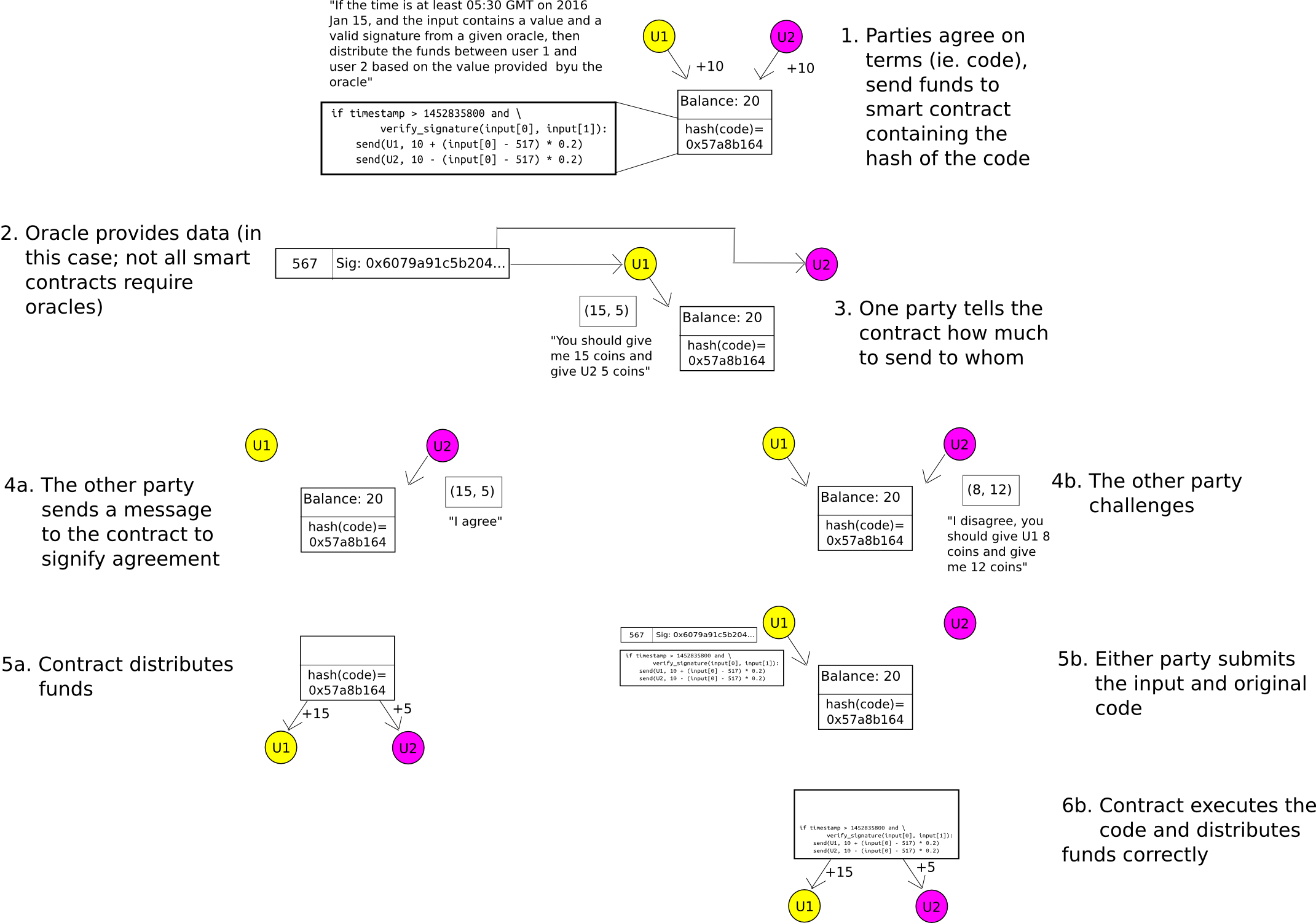
Up to now, we’ve solely mentioned token anonymization. What about two-party sensible contracts? Right here, we use the identical mechanism as Hawk, besides we substitute the cryptography with less complicated cryptoeconomics – particularly, the “auditable computation” trick. The contributors ship their funds right into a contract which shops the hash of the code. When it comes time to ship out funds, both get together can submit the consequence. The opposite get together can both ship a transaction to agree on the consequence, permitting the funds to be despatched, or it could possibly publish the precise code to the contract, at which level the code will run and distribute the funds accurately. A safety deposit can be utilized to incentivize the events to take part truthfully. Therefore, the system is non-public by default, and provided that there’s a dispute does any data get leaked to the skin world.
A generalization of this system is named state channels, and in addition has scalability advantages alongside its enhancements in privateness.
Ring Signatures
A know-how which is reasonably technically difficult, however extraordinarily promising for each token anonymization and identification purposes, is ring signatures. A hoop signature is basically a signature that proves that the signer has a non-public key similar to certainly one of a particular set of public keys, with out revealing which one. The 2-sentence clarification for a way this works mathematically is {that a} ring signature algorithm features a mathematical operate which could be computed usually with only a public key, however the place figuring out the non-public key lets you add a seed to the enter to make the output be no matter particular worth you need. The signature itself consists of an inventory of values, the place every worth is about to the operate utilized to the earlier worth (plus some seed); producing a legitimate signature requires utilizing information of a non-public key to “shut the loop”, forcing the final worth that you just compute to equal the primary. Given a legitimate “ring” produced on this manner, anybody can confirm that it’s certainly a “ring”, so every worth is the same as the operate computed on the earlier worth plus the given seed, however there isn’t a option to inform at which “hyperlink” within the ring a non-public key was used.
There may be additionally an upgraded model of a hoop signature referred to as a linkable ring signature, which provides an additional property: should you signal twice with the identical non-public key, that reality could be detected – however no different data is revealed. Within the case of token anonymization, the applying is pretty easy: when a consumer desires to spend a coin, as a substitute of getting them present a daily signature to show possession of their public key immediately, we mix public keys collectively into teams, and ask the consumer to easily show membership within the group. Due to the linkability property, a consumer that has one public key in a gaggle can solely spend from that group as soon as; conflicting signatures are rejected.
Ring signatures may also be used for voting purposes: as a substitute of utilizing ring signatures to validate spending from a set of cash, we use them to validate votes. They may also be used for identification purposes: if you wish to show that you just belong to a set of approved customers, with out revealing which one, ring signatures are well-suited for simply that. Ring signatures are extra mathematically concerned than easy signatures, however they’re fairly sensible to implement; some pattern code for ring signatures on high of Ethereum could be discovered right here.
Secret Sharing and Encryption
Typically, blockchain purposes usually are not attempting to mediate the switch of digital property, or file identification data, or course of sensible contracts, and are as a substitute getting used on extra data-centric purposes: timestamping, high-value knowledge storage, proof of existence (or proof of inexistence, as within the case of certificates revocations), and so forth. A standard chorus is the thought of utilizing blockchains to construct techniques the place “customers are answerable for their very own knowledge”.
In these instances, it’s as soon as once more essential to notice that blockchains do NOT remedy privateness points, and are an authenticity resolution solely. Therefore, placing medical information in plaintext onto a blockchain is a Very Unhealthy Thought. Nevertheless, they are often mixed with different applied sciences that do provide privateness with a view to create a holistic resolution for a lot of industries that does accomplish the specified targets, with blockchains being a vendor-neutral platform the place some knowledge could be saved with a view to present authenticity ensures.
So what are these privacy-preserving applied sciences? Nicely, within the case of straightforward knowledge storage (eg. medical information), we are able to simply use the only and oldest certainly one of all: encryption! Paperwork which are hashed on the blockchain can first be encrypted, so even when the info is saved on one thing like IPFS solely the consumer with their very own non-public key can see the paperwork. If a consumer desires to grant another person the suitable to view some particular information in decrypted type, however not all of them, one can use one thing like a deterministic pockets to derive a distinct key for every doc.
One other helpful know-how is secret sharing (described in additional element right here), permitting a consumer to encrypt a bit of knowledge in such a manner that M of a given N customers (eg. M = 5, N = 9) can cooperate to decrypt the info, however no fewer.
The Way forward for Privateness
There are two main challenges with privateness preserving protocols in blockchains. One of many challenges is statistical: to ensure that any privacy-preserving scheme to be computationally sensible, the scheme should solely alter a small a part of the blockchain state with each transaction. Nevertheless, even when the contents of the alteration are privateness, there’ll inevitably be some quantity of metadata that isn’t. Therefore, statistical analyses will at all times be capable to determine one thing; in any case, they may be capable to fish for patterns of when transactions happen, and in lots of instances they may be capable to slim down identities and determine who interacts with whom.
The second problem is the developer expertise problem. Turing-complete blockchains work very properly for builders as a result of they’re very pleasant to builders which are fully clueless concerning the underlying mechanics of decentralization: they create a decentralized “world pc” which appears to be like similar to a centralized pc, in impact saying “look, builders, you may code what you had been planning to code already, besides that this new layer on the backside will now make all the pieces magically decentralized for you”. After all, the abstraction isn’t good: excessive transaction charges, excessive latency, gasoline and block reorganizations are one thing new for programmers to cope with, however the boundaries usually are not that giant.
With privateness, as we see, there isn’t a such magic bullet. Whereas there are partial options for particular use instances, and sometimes these partial options provide a excessive diploma of flexibility, the abstractions that they current are fairly totally different from what builders are used to. It isn’t trivial to go from “10-line python script that has some code for subtracting X cash from the sender’s stability and including X cash to the recipient’s stability” to “extremely anonymized digital token utilizing linkable ring signatures”.
Initiatives like Hawk are very welcome steps in the suitable route: they provide the promise of changing an arbitrary N-party protocol right into a zero-knowledge-ified protocol that trusts solely the blockchain for authenticity, and one particular get together for privateness: primarily, combining one of the best of each worlds of a centralized and decentralized strategy. Can we go additional, and create a protocol that trusts zero events for privateness? That is nonetheless an energetic analysis route, and we’ll simply have to attend and see how far we are able to get.

